The Diffie-Hellman Key Exchange
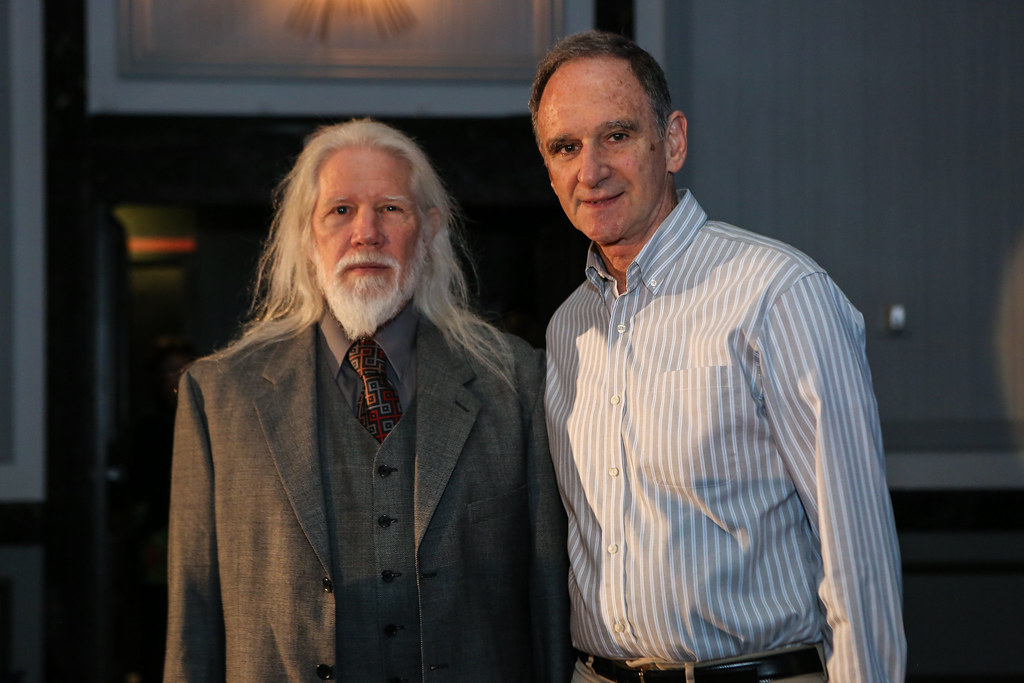
The Diffie-Hellman key exchange (DHKE) is different then most of the cryptography we have been covering in this blog. That is because we will not be using the DHKE for encrypting data, but instead as the name suggests it is a way we can exchange keys. The Diffie-Hellman key exchange was […]
Introduction to Asymmetric Cryptography

Introduction This is the beginning of asymmetric cryptography for this series of posts, so if you are just now beginning to follow along with these posts (firstly, thank you) I have good news. Very little from the posts before are needed to understand asymmetric cryptography. But that doesn’t mean we won’t ignore all […]
Introduction to Galois Fields for AES

Motivation In the next few posts I want to discuss the Advanced Encryption Standard or better known as AES, which is the most famous symmetric cipher today. But to do that unlike for DES I need to introduce a new type of mathematics. So in this post, I will introduce group […]
Stream Ciphers cont’d and Linear Feedback Shift Registers
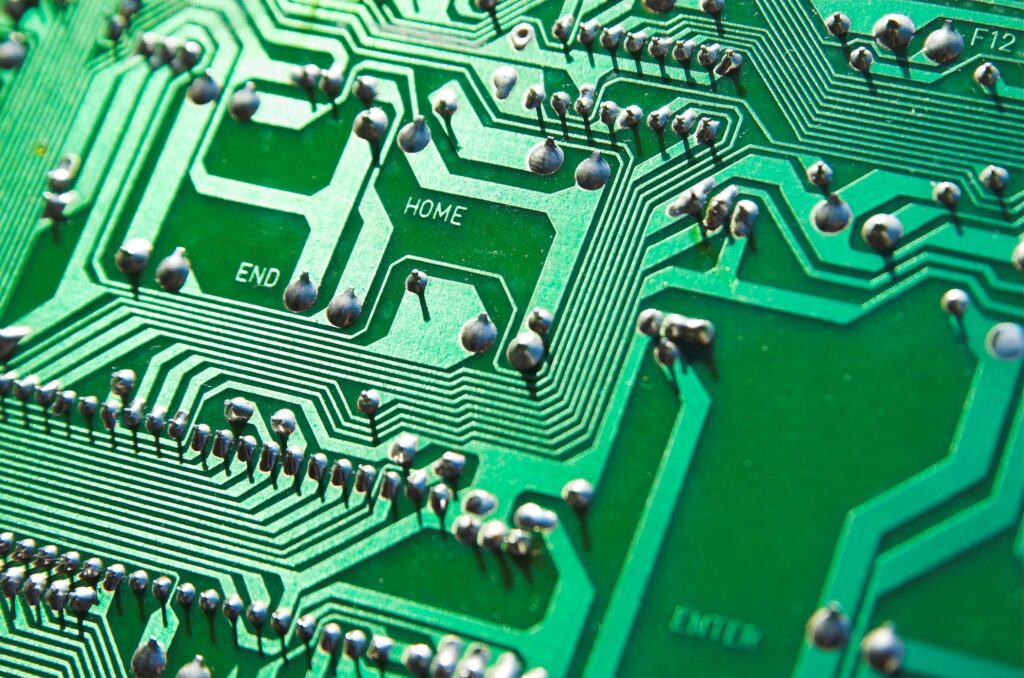
If you have not yet read the last post Stream Ciphers, Random Numbers, and the One-Time Pad it is highly recommended you go ahead and read that to understand the stream cipher. Goal: Construct a stream cipher that is small in hardware. This post makes the most sense when thinking about the hardware […]
Stream Ciphers, Random Numbers, and the One-Time Pad

Symmetric cryptography is split into two types, stream ciphers, and block ciphers. Stream ciphers encrypt one bit at a time and block ciphers encrypt multiple bits at a time. This post is dedicated to stream ciphers, if you want to learn about block ciphers make sure to read my DES and AES posts. Stream Ciphers […]
The Shift Cipher

The shift cipher, or the better-known name the Caesar cipher named after Julius Caesar is one of the simplest encryption techniques. In fact for those who have read my Substitution cipher post, the shift cipher is a type of substitution cipher where each letter in the alphabet is mapped to another fixed letter in the […]
Introduction to Modular Arithmetic

Modular Arithmetic An important question and one that I kept asking if I should dedicate a post to modular arithmetic is “Why is this important?”, and I came to conclude that while at first modular arithmetic can be very easy/ natural at first, it also gets very abstract the further into cryptography we […]
The Substitution Cipher

The Substitution Cipher We will discuss one of the simplest ciphers, the substitution cipher. This cipher has a lot of historical relevance being used many times, and is also a good starting point for cryptography and cryptanalysis. It is important to have read the What is Cryptology post because I will use concepts […]
What is Cryptology

What is Cryptology? The Oxford Dictionary defines Cryptology as: “the study of codes, or the art of writing and solving them”. When some people think of Cryptology people may think of secure website access, bank cards, or more modern “Cryptocurrency”. All of these would be correct, but cryptology is actually a much older business than […]
