The Diffie-Hellman key exchange (DHKE) is different then most of the cryptography we have been covering in this blog. That is because we
The Diffie-Hellman key exchange (DHKE) is different then most of the cryptography we have been covering in this blog. That …
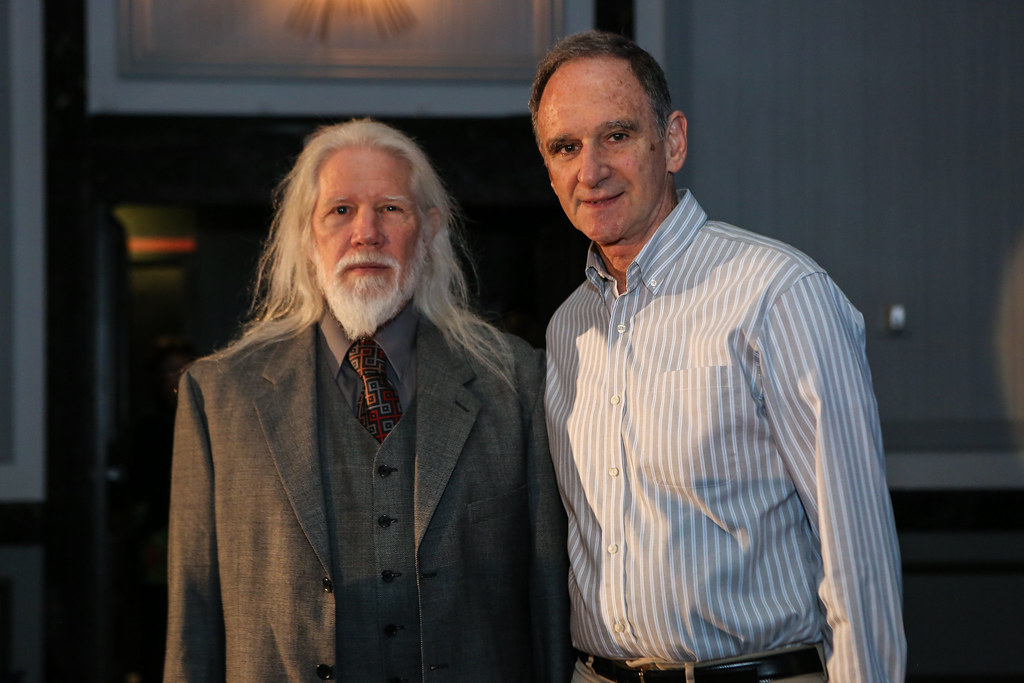
Introduction In 1976, Whitfield Diffie and Martin Hellman introduced to the world the concept of public key cryptography also known …
Introduction This is the beginning of asymmetric cryptography for this series of posts, so if you are just now beginning …
Introduction Today we won’t actually learn about any new math concepts or algorithms. Instead, we will build upon what we …
This is a continuation of (AES) The Advanced Encryption Standard [Part 1], so it is highly encouraged to read that post before …
Brief History In 1997, the National Institute of Standards and Technology (NIST) called to replace the DES. By this time …
Motivation In the next few posts I want to discuss the Advanced Encryption Standard or better known as AES, which …
This is a continuation of (DES) The Data Encryption Standard [Part 1], so it is highly encouraged to read that post before …
Introduction The Data Encryption Standard (DES) was proposed in the early 1970s by IBM, who based the design of the …
If you have not yet read the last post Stream Ciphers, Random Numbers, and the One-Time Pad it is highly recommended you …


Brief History In 1997, the National Institute of Standards and Technology (NIST) called to replace the DES. By this time DES was considered

This is a continuation of (DES) The Data Encryption Standard [Part 1], so it is highly encouraged to read that post before reading this post.

The shift cipher, or the better-known name the Caesar cipher named after Julius Caesar is one of the simplest encryption techniques. In fact for those
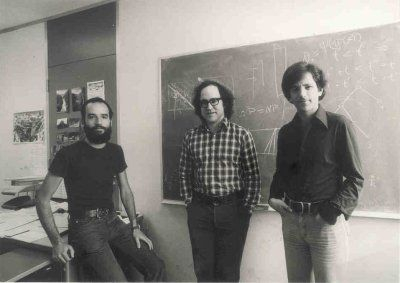
Introduction In 1976, Whitfield Diffie and Martin Hellman introduced to the world the concept of public key cryptography also known as asymmetric cryptography.
The Diffie-Hellman key exchange (DHKE) is different then most of the cryptography we have been covering in this blog. That is because we
If you have not yet read the last post Stream Ciphers, Random Numbers, and the One-Time Pad it is highly recommended you go ahead and