The Diffie-Hellman Key Exchange
The Diffie-Hellman key exchange (DHKE) is different then most of the cryptography we have been covering in this blog. That is because we will not be using the DHKE for encrypting data, but instead as the name suggests it is a way we can exchange keys. The Diffie-Hellman key exchange was […]
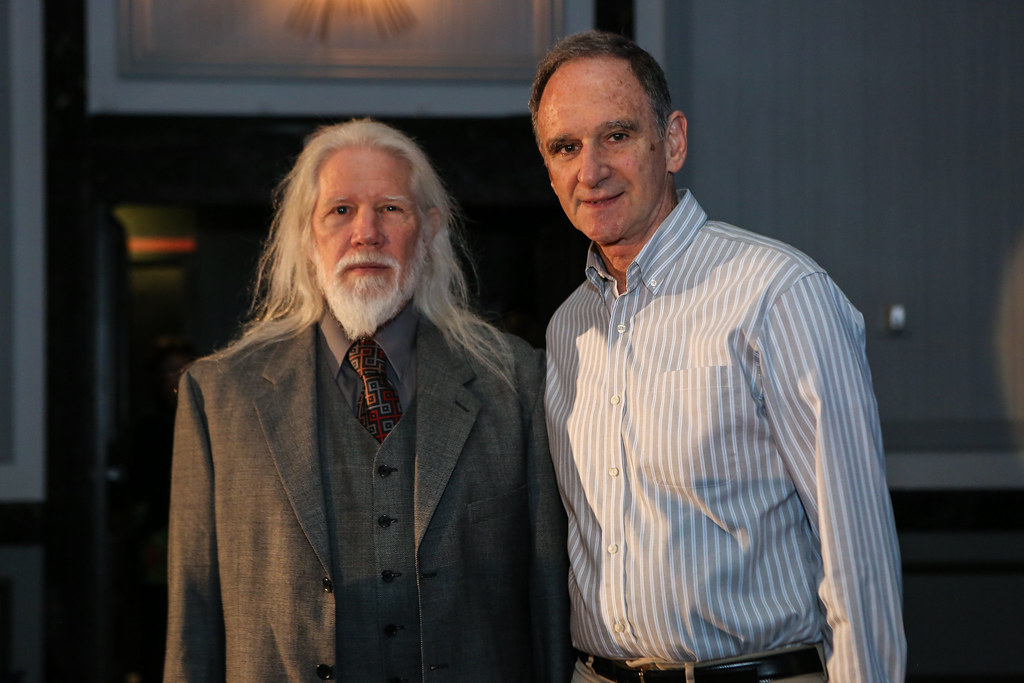
The RSA Cryptosystem
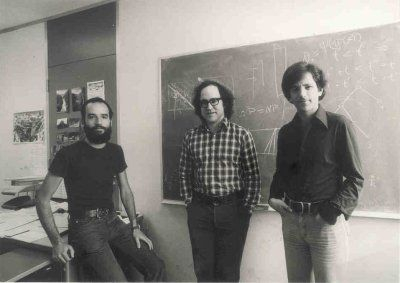
Introduction In 1976, Whitfield Diffie and Martin Hellman introduced to the world the concept of public key cryptography also known as asymmetric cryptography. But it wasn’t till 1977 when three people Ronald Rivest, Adi Shamir and Leonard Adleman proposed the scheme which would become the most used public key algorithm today called RSA. […]
Introduction to Asymmetric Cryptography

Introduction This is the beginning of asymmetric cryptography for this series of posts, so if you are just now beginning to follow along with these posts (firstly, thank you) I have good news. Very little from the posts before are needed to understand asymmetric cryptography. But that doesn’t mean we won’t ignore all […]
Modes of Operation for Block Ciphers

Introduction Today we won’t actually learn about any new math concepts or algorithms. Instead, we will build upon what we have already. Particularly how we encrypt a plaintext that is larger than a block cipher’s block size (e.g. AES 16 bytes and DES 8 bytes). In practice, we typically want to encrypt more […]
(AES) Key Schedule and Decryption [Part 2]

This is a continuation of (AES) The Advanced Encryption Standard [Part 1], so it is highly encouraged to read that post before reading this post. In that post, I gave the history of AES and also explained the internals of the AES algorithm. In this post we will discuss these things: The AES […]
(AES) The Advanced Encryption Standard [Part 1]

Brief History In 1997, the National Institute of Standards and Technology (NIST) called to replace the DES. By this time DES was considered dying because of its small key space discussed in the DES post. This was unlike when DES was designed because the selection of the AES algorithm was an open-source process. […]
Introduction to Galois Fields for AES

Motivation In the next few posts I want to discuss the Advanced Encryption Standard or better known as AES, which is the most famous symmetric cipher today. But to do that unlike for DES I need to introduce a new type of mathematics. So in this post, I will introduce group […]
(DES) Key Schedule and Decryption [Part 2]

This is a continuation of (DES) The Data Encryption Standard [Part 1], so it is highly encouraged to read that post before reading this post. In that post I gave the history of DES and also explained the internals of the DES algorithm. In this post we will discuss two things: The DES […]
(DES) The Data Encryption Standard [Part 1]
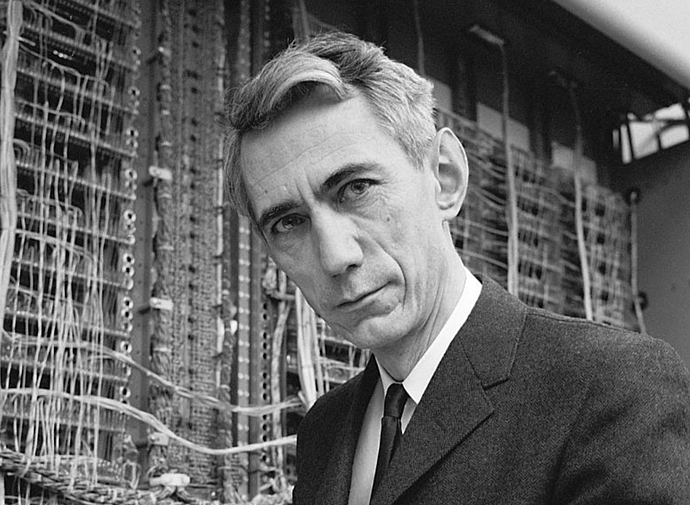
Introduction The Data Encryption Standard (DES) was proposed in the early 1970s by IBM, who based the design of the cipher on an earlier design by Horst Feistel. The cipher was created as a request by the United States National Bureau of Standards (NBS) which is the modern-day National Institute of Standards and […]
Stream Ciphers cont’d and Linear Feedback Shift Registers
If you have not yet read the last post Stream Ciphers, Random Numbers, and the One-Time Pad it is highly recommended you go ahead and read that to understand the stream cipher. Goal: Construct a stream cipher that is small in hardware. This post makes the most sense when thinking about the hardware […]
